Official 2014 Latest Microsoft 70-410 Exam Dump Free Download(301-310)!
QUESTION 301
Hotspot Question
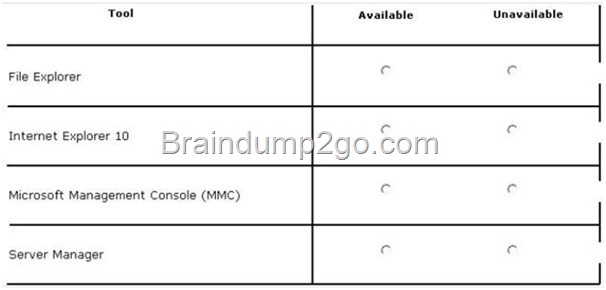
Your network contains an Active Directory domain named contoso.com. The domain contains a print server named Print1 that runs Windows Server 2012 R2. Print1 has 50 shared printers. Each printer is listed in Active Directory. From Active Directory Users and Computers, you browse to Print1 and you discover that the 50 printers are not visible. You need to ensure that you can view the printer objects in Active Directory Users and Computers. Which option should you select?To answer, select the appropriate option in the answer area.
![clip_image001[18] clip_image001[18]](http://examgod.com/l2pimages/5bae3a6b6b06_76F1/clip_image00118_thumb.jpg)
Answer:
![clip_image001[20] clip_image001[20]](http://examgod.com/l2pimages/5bae3a6b6b06_76F1/clip_image00120_thumb.jpg)
QUESTION 302
You have a file server named File1 that runs Windows Server 2012 R2. File1 contains a shared folder named Share1. Share1 contains an Application named SalesApp1.exe. The NTFS permissions for Share1 are shown in the following table.
![clip_image001[22] clip_image001[22]](http://examgod.com/l2pimages/5bae3a6b6b06_76F1/clip_image00122_thumb.jpg)
The members of L_Sales discover that they cannot add files to Share1. Domain users can run SalesApp1.exe successfully. You need to ensure that the members of L_Sales can add files to Share1.
What should you do?
A. Add the Domain Users group to L_Sales.
B. Add L_Sales to the Domain Users group.
C. Edit the Share permissions.
D. Edit the NTFS permissions.
Answer: C
Explanation:
http://www.techrepublic.com/article/windows-101-know-the-basics-about-ntfs-permissions/
The least restrictive permission applies here, so the users from L_sales have read & execute, write… in order to add files they need the NTFS permission called MODIFY.
Based on NTFS permissions:
Modify: Users can view and modify files and file properties, including deleting and adding files to a directory or file properties to a file.
QUESTION 303
Hotspot Question
You have a file server named Server1 that runs Windows Server 2012 R2. Server1 contains a folder named Folder1.
![clip_image001[24] clip_image001[24]](http://examgod.com/l2pimages/5bae3a6b6b06_76F1/clip_image00124_thumb.jpg)
A user named User1 is a member of Group1 and Group2. A user named User2 is a member of Group2 and Group3. You need to identify which actions the users can perform when they access the files in Share1. What should you identify? To answer, select the appropriate actions for each user in the answer area.
QUESTION 304
Your network contains an Active Directory domain named contoso.com. The domain contains two servers named Server1 and Server2 that run Windows Server 2012 R2. Server1 has the Group Policy Management feature installed. Server2 has the Print and Document Services server role installed. On Server2, you open Print Management and you deploy a printer named Printer1 by using a Group Policy object (GPO) named GPO1. When you open GPO1 on Server1, you discover that the Deployed Printers node does not appear. You need to view the Deployed Printers node in GPO1. What should you do?
A. On Server1, modify the Group Policy filtering options of GPO1.
B. On a domain controller, create a Group Policy central store.
C. On Server2, install the Group Policy Management feature.
D. On Server1, configure the security filtering of GPO1.
Answer: C
Explanation:
Pre-Requisites
To use Group Policy for printer deployment you will need to have a Windows Active Directory domain, and this article assumes that your Domain Controller is a Windows 2008 R2 Server. You will also need the Print Services role installed on a server (can be on your DC), and you will be using the Print Management and Group Policy Management consoles to configure the various settings. Its assumed that you have already followed Part One and have one or more printers shared on your server with the necessary drivers, ready to deploy to your client computers.
The wording does not say if GPMC is installed on server 2, so I can only think that it does not deploy the GPO because it had no GPMC on server 2..
GPMC is not installed by default:
http://pipe2text.com/?page_id=1591
http://technet.microsoft.com/en-us/library/cc725932.aspx
QUESTION 305
Your network contains an Active Directory domain named contoso.com. All of the App1ocker policy settings for the member servers are configured in a Group Policy object (GPO) named GPO1. A member server named Server1 runs Windows Server 2012 R2. On Server1, you test a new set of App1ocker policy settings by using a local computer policy. You need to merge the local App1ocker policy settings from Server1 into the App1ocker policy settings of GPO1. What should you do?
A. From Local Group Policy Editor on Server1, exportan .xml file. Import the .xml file by using Group
Policy Management Editor.
B. From Local Group Policy Editor on Server1, exportan .inf file. Import the .inf file by using Group Policy
Management Editor.
C. From Server1, run the Set-App1ockerPolicy cmdlet.
D. From Server1, run the New-App1ockerPolicy cmdlet.
Answer: C
Explanation:
http://technet.microsoft.com/en-us/library/ee791816(v=ws.10).aspx
The Set-AppLockerPolicy cmdlet sets the specified Group Policy Object (GPO) to contain the specified AppLocker policy. If no Lightweight Directory Access Protocol (LDAP) is specified, the local GPO is the default. When the Merge parameter is used, rules in the specified AppLocker policy will be merged with the AppLocker rules in the target GPO specified in the LDAP path. The merging of policies will remove rules with duplicate rule IDs, and the enforcement setting specified by the AppLocker policy in the target GPO will be preserved. If the Merge parameter is not specified, then the new policy will overwrite the existing policy.
QUESTION 306
Your network contains an Active Directory domain named contoso.com. You have a Group Policy object (GPO) named GP1 that is linked to the domain. GP1 contains a software restriction policy that blocks an Application named App1. You have a workgroup computer named Computer1 that runs Windows 8. A local Group Policy on Computer1 contains an Application control policy that allows App1. You join Computer1 to the domain. You need to prevent App1 from running on Computer1.
What should you do?
A. From Group Policy Management, add an Application control policy to GP1.
B. From Group Policy Management, enable the Enforced option on GP1.
C. In the local Group Policy of Computer1, configure a software restriction policy.
D. From Computer1, run gpupdate /force.
Answer: D
Explanation:
http://technet.microsoft.com/en-us/library/cc785665(v=ws.10).aspx
Order of processing settings
This section provides details about the order in which Group Policy settings for users and computers are processed.
Group Policy settings are processed in the following order:
1.Local Group Policy object—Each computer has exactly one Group Policy object that is stored locally. This processes for both computer and user Group Policy processing.
2.Site—Any GPOs that have been linked to the site that the computer belongs to are processed next.
3.Domain—Processing of multiple domain-linked GPOs is in the order specified by the administrator, on the Linked Group Policy Objects tab for the domain in GPMC.
4.Organizational units—GPOs that are linked to the organizational unit that is highest in the Active Directory hierarchy are processed first, then GPOs that are linked to its child organizational unit, and so on. Finally, the GPOs that are linked to the organizational unit that contains the user or computer are processed.
This order means that the local GPO is processed first, and GPOs that are linked to the organizational unit of which the computer or user is a direct member are processed last, **which overwrites settings in the earlier GPOs if there are conflicts.** (If there are no conflicts, then the earlier and later settings are merely aggregated.)
QUESTION 307
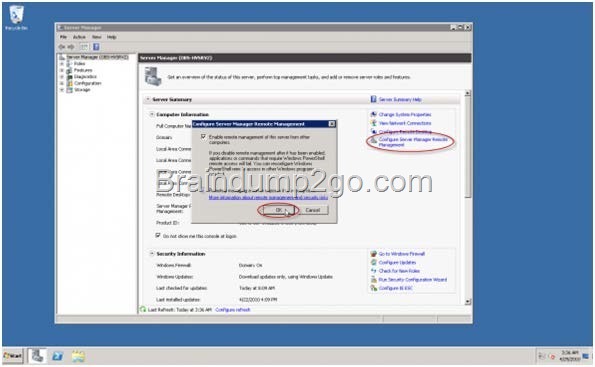
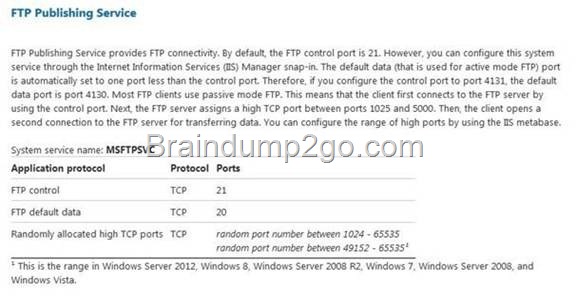
Your network contains an Active Directory domain named contoso.com. The domain contains an Application server named Server1. Server1 runs Windows Server 2012 R2. Server1 is configured as an FTP server. Client computers use an FTP Application named App1.exe. App1.exe uses TCP port 21 as the control port and dynamically requests a data port. On Server1, you create a firewall rule to allow connections on TCP port 21. You need to configure Server1 to support the client connections from App1.exe. What should you do?
A. Run netsh firewall addportopening TCP 21 dynamicftp.
B. Create a tunnel connection security rule.
C. Create an outbound firewall rule to allow App1.exe.
D. Run netshadvfirewall set global statefulftp enable.
Answer: D
Explanation:
http://technet.microsoft.com/en-us/library/cc771920%28v=ws.10%29.aspx#BKMK_set_2a
The netsh firewall context is supplied only for backward compatibility. We recommend that you do not use this context on a computer that is running Windows Vista or a later version of Windows
In the netsh advfirewall firewall context, the add command only has one variation, the add rule command.
Netsh advfirewall set global statefulftp:
Configures how Windows Firewall with Advanced Security handles FTP traffic that uses an initial connection on one port to request a data connection on a different port.
When statefulftp is enabled, the firewall examines the PORT and PASV requests for these other port numbers and then allows the corresponding data connection to the port number that was requested.
Syntax
set global statefulftp { enable | disable | notconfigured }
Parameters
statefulftp can be set to one of the following values:
enable The firewall tracks the port numbers specified in PORT command requests and in the responses to PASV requests, and then allows the incoming FTP data traffic entering on the requested port number.
disable
This is the default value. The firewall does not track outgoing PORT commands or PASV responses, and so incoming data connections on the PORT or PASV requested port is blocked as an unsolicited incoming connection.
notconfigured
Valid only when netsh is configuring a GPO by using the set store command.
QUESTION 308
Hotspot Question
Your network contains an Active Directory domain named contoso.com. The domain contains an organizational unit (OU) named OU1 as shown in the OU1 exhibit. (Click the Exhibit button.)
![clip_image001[30] clip_image001[30]](http://examgod.com/l2pimages/5bae3a6b6b06_76F1/clip_image00130_thumb.jpg)
The membership of Group1 is shown in the Group1 exhibit. (Click the Exhibit button.)
![clip_image001[32] clip_image001[32]](http://examgod.com/l2pimages/5bae3a6b6b06_76F1/clip_image00132_thumb.jpg)
You configure GPO1 to prohibit access to Control Panel. GPO1 is linked to OU1 as shown in the GPO1 exhibit. (Click the Exhibit button.)
![clip_image001[34] clip_image001[34]](http://examgod.com/l2pimages/5bae3a6b6b06_76F1/clip_image00134_thumb.jpg)
Select Yes if the statement can be shown to be true based on the available information; otherwise select No. Each correct selection is worth one point.
![clip_image001[36] clip_image001[36]](http://examgod.com/l2pimages/5bae3a6b6b06_76F1/clip_image00136_thumb.jpg)
Answer:
![clip_image001[38] clip_image001[38]](http://examgod.com/l2pimages/5bae3a6b6b06_76F1/clip_image00138_thumb.jpg)
QUESTION 309
Your company has a main office and four branch offices. The main office contains a server named Server1 that runs Windows Server 2012 R2. The IP configuration of each office is configured as shown in the following table.
![clip_image001[40] clip_image001[40]](http://examgod.com/l2pimages/5bae3a6b6b06_76F1/clip_image00140_thumb.jpg)
You need to add a single static route on Server1 to ensure that Server1 can communicate with the hosts on all of the subnets. Which command should you run?
A. route.exe add -p 192.168.0.0 mask 255.255.248.0 172.31.255.254
B. route.exe add -p 192.168.12.0 mask 255.255.252.0 172.31.255.254
C. route.exe add -p 192.168.8.0 mask 255.255.252.0 172.31.255.254
D. route.exe add -p 192.168.12.0 mask 255.255.255.0 172.31.255.254
Answer: B
QUESTION 310
You work as an administrator at L2P.com. The L2P.com network consists of a single domain named L2P.com. All servers in the L2P.com domain, including domain controllers, have Windows Server 2012 R2 installed.
You have created and linked a new Group Policy object (GPO) to an organizational unit (OU), named L2PServ, which host the computer accounts for servers in the L2P.com domain.
You have been tasked with adding a group to a local group on all servers in the L2P.com domain. This group should not, however, be removed from the local group.
Which of the following actions should you take?
A. You should consider adding a restricted group.
B. You should consider adding a global group.
C. You should consider adding a user group.
D. You should consider adding a server group.
Answer: A
Explanation:
Restricted groups in Group policies are a simple way of delegating permissions or group membership centrally to any domain computer or server. Using restricted groups it is easier to enforce the lowest possible permissions to any given account.
Computer Configuration\Windows Settings\Security Settings\Restricted Groups
Restricted groups allow an administrator to define two properties for security-sensitive groups (that is, “restricted” groups). The two properties are Members and Member Of .
The Members list defines who should and should not belong to the restricted group.
The Member Of list specifies which other groups the restricted group should belong to. When a restricted Group Policy is enforced, any current member of a restricted group that is not on the Members list is removed. Any user on the Members list which is not currently a member of the restricted group is added. The Restricted Groups folder is available only in Group Policy objects associated with domains, OUs, and sites. The Restricted Groups folder does not appear in the Local Computer Policy object. If a Restricted Group is defined such that it has no members (that is, the Members list is empty), then all members of the group are removed when the policy is enforced on the system. If the Member Of list is empty no changes are made to any groups that the restricted group belongs to. In short, an empty Members list means the restricted group should have no members while an empty Member Of list means “don’t care” what groups the restricted group belongs to.
![clip_image002[22] clip_image002[22]](http://examgod.com/l2pimages/5bae3a6b6b06_76F1/clip_image00222_thumb.jpg)
http://technet.microsoft.com/en-us/library/cc957640.aspx
Passing Microsoft 70-410 Exam successfully in a short time! Just using Braindump2go’s Latest Microsoft 70-410 Dump:
![clip_image001[26] clip_image001[26]](http://examgod.com/l2pimages/5bae3a6b6b06_76F1/clip_image00126_thumb.jpg)
![clip_image001[28] clip_image001[28]](http://examgod.com/l2pimages/5bae3a6b6b06_76F1/clip_image00128_thumb.jpg)
![clip_image002[10] clip_image002[10]](http://examgod.com/l2pimages/5bae3a6b6b06_76F1/clip_image00210_thumb.jpg)
![clip_image002[12] clip_image002[12]](http://examgod.com/l2pimages/5bae3a6b6b06_76F1/clip_image00212_thumb.jpg)
![clip_image002[14] clip_image002[14]](http://examgod.com/l2pimages/5bae3a6b6b06_76F1/clip_image00214_thumb.jpg)
![clip_image001[10] clip_image001[10]](http://examgod.com/l2pimages/5bae3a6b6b06_76F1/clip_image00110_thumb.jpg)
![clip_image001[12] clip_image001[12]](http://examgod.com/l2pimages/5bae3a6b6b06_76F1/clip_image00112_thumb.jpg)
![clip_image001[14] clip_image001[14]](http://examgod.com/l2pimages/5bae3a6b6b06_76F1/clip_image00114_thumb.jpg)
![clip_image002[16] clip_image002[16]](http://examgod.com/l2pimages/5bae3a6b6b06_76F1/clip_image00216_thumb.jpg)
![clip_image002[18] clip_image002[18]](http://examgod.com/l2pimages/5bae3a6b6b06_76F1/clip_image00218_thumb.jpg)
![clip_image002[20] clip_image002[20]](http://examgod.com/l2pimages/5bae3a6b6b06_76F1/clip_image00220_thumb.jpg)
![clip_image001[16] clip_image001[16]](http://examgod.com/l2pimages/5bae3a6b6b06_76F1/clip_image00116_thumb.jpg)
![clip_image001[4] clip_image001[4]](http://examgod.com/l2pimages/5bae3a6b6b06_76F1/clip_image0014_thumb.jpg)
![clip_image002[4] clip_image002[4]](http://examgod.com/l2pimages/5bae3a6b6b06_76F1/clip_image0024_thumb.jpg)
![clip_image001[6] clip_image001[6]](http://examgod.com/l2pimages/5bae3a6b6b06_76F1/clip_image0016_thumb.jpg)
![clip_image002[6] clip_image002[6]](http://examgod.com/l2pimages/5bae3a6b6b06_76F1/clip_image0026_thumb.jpg)
![clip_image001[8] clip_image001[8]](http://examgod.com/l2pimages/5bae3a6b6b06_76F1/clip_image0018_thumb.jpg)
![clip_image002[8] clip_image002[8]](http://examgod.com/l2pimages/5bae3a6b6b06_76F1/clip_image0028_thumb_3.jpg)
![clip_image001[87] clip_image001[87]](http://examgod.com/l2pimages/81e1d59efa0a_7768/clip_image00187_thumb.jpg)
![clip_image002[62] clip_image002[62]](http://examgod.com/l2pimages/81e1d59efa0a_7768/clip_image00262_thumb.jpg)
![clip_image002[64] clip_image002[64]](http://examgod.com/l2pimages/81e1d59efa0a_7768/clip_image00264_thumb.jpg)
![clip_image001[89] clip_image001[89]](http://examgod.com/l2pimages/81e1d59efa0a_7768/clip_image00189_thumb.jpg)
![clip_image002[66] clip_image002[66]](http://examgod.com/l2pimages/81e1d59efa0a_7768/clip_image00266_thumb.jpg)
![clip_image002[68] clip_image002[68]](http://examgod.com/l2pimages/81e1d59efa0a_7768/clip_image00268_thumb.jpg)
![clip_image001[91] clip_image001[91]](http://examgod.com/l2pimages/81e1d59efa0a_7768/clip_image00191_thumb.jpg)
![clip_image002[54] clip_image002[54]](http://examgod.com/l2pimages/81e1d59efa0a_7768/clip_image00254_thumb.jpg)
![clip_image002[56] clip_image002[56]](http://examgod.com/l2pimages/81e1d59efa0a_7768/clip_image00256_thumb.jpg)
![clip_image001[81] clip_image001[81]](http://examgod.com/l2pimages/81e1d59efa0a_7768/clip_image00181_thumb.jpg)
![clip_image001[83] clip_image001[83]](http://examgod.com/l2pimages/81e1d59efa0a_7768/clip_image00183_thumb.jpg)
![clip_image002[58] clip_image002[58]](http://examgod.com/l2pimages/81e1d59efa0a_7768/clip_image00258_thumb.jpg)
![clip_image002[60] clip_image002[60]](http://examgod.com/l2pimages/81e1d59efa0a_7768/clip_image00260_thumb.jpg)
![clip_image001[85] clip_image001[85]](http://examgod.com/l2pimages/81e1d59efa0a_7768/clip_image00185_thumb.jpg)
![clip_image001[65] clip_image001[65]](http://examgod.com/l2pimages/81e1d59efa0a_7768/clip_image00165_thumb.jpg)
![clip_image001[67] clip_image001[67]](http://examgod.com/l2pimages/81e1d59efa0a_7768/clip_image00167_thumb.jpg)
![clip_image001[69] clip_image001[69]](http://examgod.com/l2pimages/81e1d59efa0a_7768/clip_image00169_thumb.jpg)
![clip_image001[71] clip_image001[71]](http://examgod.com/l2pimages/81e1d59efa0a_7768/clip_image00171_thumb.jpg)
![clip_image001[73] clip_image001[73]](http://examgod.com/l2pimages/81e1d59efa0a_7768/clip_image00173_thumb.jpg)
![clip_image002[38] clip_image002[38]](http://examgod.com/l2pimages/81e1d59efa0a_7768/clip_image00238_thumb.jpg)
![clip_image002[40] clip_image002[40]](http://examgod.com/l2pimages/81e1d59efa0a_7768/clip_image00240_thumb.jpg)
![clip_image002[42] clip_image002[42]](http://examgod.com/l2pimages/81e1d59efa0a_7768/clip_image00242_thumb.jpg)
![clip_image002[44] clip_image002[44]](http://examgod.com/l2pimages/81e1d59efa0a_7768/clip_image00244_thumb.jpg)
![clip_image001[75] clip_image001[75]](http://examgod.com/l2pimages/81e1d59efa0a_7768/clip_image00175_thumb.jpg)
![clip_image002[46] clip_image002[46]](http://examgod.com/l2pimages/81e1d59efa0a_7768/clip_image00246_thumb.jpg)
![clip_image002[48] clip_image002[48]](http://examgod.com/l2pimages/81e1d59efa0a_7768/clip_image00248_thumb.jpg)
![clip_image002[50] clip_image002[50]](http://examgod.com/l2pimages/81e1d59efa0a_7768/clip_image00250_thumb.jpg)
![clip_image002[52] clip_image002[52]](http://examgod.com/l2pimages/81e1d59efa0a_7768/clip_image00252_thumb.jpg)
![clip_image001[77] clip_image001[77]](http://examgod.com/l2pimages/81e1d59efa0a_7768/clip_image00177_thumb.jpg)
![clip_image001[79] clip_image001[79]](http://examgod.com/l2pimages/81e1d59efa0a_7768/clip_image00179_thumb.jpg)
![clip_image001[55] clip_image001[55]](http://examgod.com/l2pimages/81e1d59efa0a_7768/clip_image00155_thumb.jpg)
![clip_image001[57] clip_image001[57]](http://examgod.com/l2pimages/81e1d59efa0a_7768/clip_image00157_thumb.jpg)
![clip_image002[30] clip_image002[30]](http://examgod.com/l2pimages/81e1d59efa0a_7768/clip_image00230_thumb.jpg)
![clip_image002[32] clip_image002[32]](http://examgod.com/l2pimages/81e1d59efa0a_7768/clip_image00232_thumb.jpg)
![clip_image001[59] clip_image001[59]](http://examgod.com/l2pimages/81e1d59efa0a_7768/clip_image00159_thumb.jpg)
![clip_image002[36] clip_image002[36]](http://examgod.com/l2pimages/81e1d59efa0a_7768/clip_image00236_thumb.jpg)
![clip_image001[61] clip_image001[61]](http://examgod.com/l2pimages/81e1d59efa0a_7768/clip_image00161_thumb.jpg)
![clip_image001[63] clip_image001[63]](http://examgod.com/l2pimages/81e1d59efa0a_7768/clip_image00163_thumb.jpg)
![clip_image001[33] clip_image001[33]](http://examgod.com/l2pimages/81e1d59efa0a_7768/clip_image00133_thumb.jpg)
![clip_image002[18] clip_image002[18]](http://examgod.com/l2pimages/81e1d59efa0a_7768/clip_image00218_thumb.jpg)
![clip_image001[35] clip_image001[35]](http://examgod.com/l2pimages/81e1d59efa0a_7768/clip_image00135_thumb.jpg)
![clip_image001[37] clip_image001[37]](http://examgod.com/l2pimages/81e1d59efa0a_7768/clip_image00137_thumb.jpg)
![clip_image001[39] clip_image001[39]](http://examgod.com/l2pimages/81e1d59efa0a_7768/clip_image00139_thumb.jpg)
![clip_image001[41] clip_image001[41]](http://examgod.com/l2pimages/81e1d59efa0a_7768/clip_image00141_thumb.jpg)
![clip_image002[20] clip_image002[20]](http://examgod.com/l2pimages/81e1d59efa0a_7768/clip_image00220_thumb.jpg)
![clip_image002[22] clip_image002[22]](http://examgod.com/l2pimages/81e1d59efa0a_7768/clip_image00222_thumb.jpg)
![clip_image002[24] clip_image002[24]](http://examgod.com/l2pimages/81e1d59efa0a_7768/clip_image00224_thumb.jpg)
![clip_image002[26] clip_image002[26]](http://examgod.com/l2pimages/81e1d59efa0a_7768/clip_image00226_thumb.jpg)
![clip_image002[28] clip_image002[28]](http://examgod.com/l2pimages/81e1d59efa0a_7768/clip_image00228_thumb.jpg)
![clip_image001[43] clip_image001[43]](http://examgod.com/l2pimages/81e1d59efa0a_7768/clip_image00143_thumb.jpg)
![clip_image001[45] clip_image001[45]](http://examgod.com/l2pimages/81e1d59efa0a_7768/clip_image00145_thumb.jpg)
![clip_image001[47] clip_image001[47]](http://examgod.com/l2pimages/81e1d59efa0a_7768/clip_image00147_thumb.jpg)
![clip_image001[49] clip_image001[49]](http://examgod.com/l2pimages/81e1d59efa0a_7768/clip_image00149_thumb.jpg)
![clip_image001[51] clip_image001[51]](http://examgod.com/l2pimages/81e1d59efa0a_7768/clip_image00151_thumb.jpg)
![clip_image001[53] clip_image001[53]](http://examgod.com/l2pimages/81e1d59efa0a_7768/clip_image00153_thumb.jpg)
![clip_image001[25] clip_image001[25]](http://examgod.com/l2pimages/81e1d59efa0a_7768/clip_image00125_thumb.jpg)
![clip_image002[12] clip_image002[12]](http://examgod.com/l2pimages/81e1d59efa0a_7768/clip_image00212_thumb.jpg)
![clip_image001[27] clip_image001[27]](http://examgod.com/l2pimages/81e1d59efa0a_7768/clip_image00127_thumb.jpg)
![clip_image001[29] clip_image001[29]](http://examgod.com/l2pimages/81e1d59efa0a_7768/clip_image00129_thumb.jpg)
![clip_image002[14] clip_image002[14]](http://examgod.com/l2pimages/81e1d59efa0a_7768/clip_image00214_thumb.jpg)
![clip_image001[31] clip_image001[31]](http://examgod.com/l2pimages/81e1d59efa0a_7768/clip_image00131_thumb.jpg)
![clip_image002[16] clip_image002[16]](http://examgod.com/l2pimages/81e1d59efa0a_7768/clip_image00216_thumb.jpg)
![clip_image001[12] clip_image001[12]](http://examgod.com/l2pimages/81e1d59efa0a_7768/clip_image00112_thumb.jpg)
![clip_image001[14] clip_image001[14]](http://examgod.com/l2pimages/81e1d59efa0a_7768/clip_image00114_thumb.jpg)
![clip_image002[6] clip_image002[6]](http://examgod.com/l2pimages/81e1d59efa0a_7768/clip_image0026_thumb.jpg)
![clip_image001[16] clip_image001[16]](http://examgod.com/l2pimages/81e1d59efa0a_7768/clip_image00116_thumb.jpg)
![clip_image001[18] clip_image001[18]](http://examgod.com/l2pimages/81e1d59efa0a_7768/clip_image00118_thumb.jpg)
![clip_image001[21] clip_image001[21]](http://examgod.com/l2pimages/81e1d59efa0a_7768/clip_image00121_thumb.jpg)
![clip_image001[23] clip_image001[23]](http://examgod.com/l2pimages/81e1d59efa0a_7768/clip_image00123_thumb.jpg)
![clip_image002[8] clip_image002[8]](http://examgod.com/l2pimages/81e1d59efa0a_7768/clip_image0028_thumb.jpg)
![clip_image002[10] clip_image002[10]](http://examgod.com/l2pimages/81e1d59efa0a_7768/clip_image00210_thumb.jpg)
![clip_image001[4] clip_image001[4]](http://examgod.com/l2pimages/81e1d59efa0a_7768/clip_image0014_thumb.jpg)
![clip_image001[6] clip_image001[6]](http://examgod.com/l2pimages/81e1d59efa0a_7768/clip_image0016_thumb.jpg)
![clip_image001[8] clip_image001[8]](http://examgod.com/l2pimages/81e1d59efa0a_7768/clip_image0018_thumb.jpg)
![clip_image001[10] clip_image001[10]](http://examgod.com/l2pimages/81e1d59efa0a_7768/clip_image00110_thumb.jpg)
![clip_image002[4] clip_image002[4]](http://examgod.com/l2pimages/81e1d59efa0a_7768/clip_image0024_thumb.jpg)
![clip_image002[6] clip_image002[6]](http://examgod.com/l2pimages/2edfea847c6e_7912/clip_image0026_thumb_5.jpg)
![clip_image001[6] clip_image001[6]](http://examgod.com/l2pimages/2edfea847c6e_7912/clip_image0016_thumb_5.jpg)
![clip_image001[8] clip_image001[8]](http://examgod.com/l2pimages/2edfea847c6e_7912/clip_image0018_thumb_5.jpg)
![clip_image001[10] clip_image001[10]](http://examgod.com/l2pimages/2edfea847c6e_7912/clip_image00110_thumb_5.jpg)
![clip_image001[12] clip_image001[12]](http://examgod.com/l2pimages/2edfea847c6e_7912/clip_image00112_thumb_5.jpg)
![clip_image001[14] clip_image001[14]](http://examgod.com/l2pimages/2edfea847c6e_7912/clip_image00114_thumb_4.jpg)
![clip_image002[4] clip_image002[4]](http://examgod.com/l2pimages/2edfea847c6e_7912/clip_image0024_thumb_5.jpg)
![clip_image001[4] clip_image001[4]](http://examgod.com/l2pimages/2edfea847c6e_7912/clip_image0014_thumb_5.jpg)
![clip_image001[24] clip_image001[24]](http://examgod.com/l2pimages/2edfea847c6e_7912/clip_image00124_thumb_3.jpg)
![clip_image002[6] clip_image002[6]](http://examgod.com/l2pimages/2edfea847c6e_7912/clip_image0026_thumb_4.jpg)
![clip_image002[8] clip_image002[8]](http://examgod.com/l2pimages/2edfea847c6e_7912/clip_image0028_thumb_4.jpg)
![clip_image002[10] clip_image002[10]](http://examgod.com/l2pimages/2edfea847c6e_7912/clip_image00210_thumb_3.jpg)
![clip_image002[12] clip_image002[12]](http://examgod.com/l2pimages/2edfea847c6e_7912/clip_image00212_thumb_3.jpg)
![clip_image002[14] clip_image002[14]](http://examgod.com/l2pimages/2edfea847c6e_7912/clip_image00214_thumb_3.jpg)
![clip_image001[26] clip_image001[26]](http://examgod.com/l2pimages/2edfea847c6e_7912/clip_image00126_thumb_3.jpg)
![clip_image001[4] clip_image001[4]](http://examgod.com/l2pimages/2edfea847c6e_7912/clip_image0014_thumb_4.jpg)
![clip_image001[6] clip_image001[6]](http://examgod.com/l2pimages/2edfea847c6e_7912/clip_image0016_thumb_4.jpg)
![clip_image001[8] clip_image001[8]](http://examgod.com/l2pimages/2edfea847c6e_7912/clip_image0018_thumb_4.jpg)
![clip_image001[10] clip_image001[10]](http://examgod.com/l2pimages/2edfea847c6e_7912/clip_image00110_thumb_4.jpg)
![clip_image001[12] clip_image001[12]](http://examgod.com/l2pimages/2edfea847c6e_7912/clip_image00112_thumb_4.jpg)
![clip_image001[14] clip_image001[14]](http://examgod.com/l2pimages/2edfea847c6e_7912/clip_image00114_thumb_3.jpg)
![clip_image001[16] clip_image001[16]](http://examgod.com/l2pimages/2edfea847c6e_7912/clip_image00116_thumb_3.jpg)
![clip_image001[18] clip_image001[18]](http://examgod.com/l2pimages/2edfea847c6e_7912/clip_image00118_thumb_3.jpg)
![clip_image001[20] clip_image001[20]](http://examgod.com/l2pimages/2edfea847c6e_7912/clip_image00120_thumb_3.jpg)
![clip_image002[4] clip_image002[4]](http://examgod.com/l2pimages/2edfea847c6e_7912/clip_image0024_thumb_4.jpg)
![clip_image001[22] clip_image001[22]](http://examgod.com/l2pimages/2edfea847c6e_7912/clip_image00122_thumb_3.jpg)