Official 2014 Latest Microsoft 70-410 Exam Dump Free Download(111-120)!
QUESTION 111
Your company has a remote office that contains 1,600 client computers on a single subnet.
You need to select a subnet mask for the network that will support all of the client computers. The solution must minimize the number of unused addresses. Which subnet mask should you select?
A. 255.255.248.0
B. 255.255.252.0
C. 255.255.254.0
D. 255.255.240.0
Answer: A
Explanation:
255.255.252.0 = 11111111.11111111.11111100.00000000 =>( 22 bits 1 .. 10 bits 0 ) => 1111111111 = 1023
255.255.254.0 = 11111111.11111111.11111110.00000000 =>( 23 bits 1 .. 9 bits 0 ) => 111111111 = 511
255.255.255.0 = 11111111.11111111.11111111.00000000 =>( 24 bits 1 .. 8 bits 0 ) => 11111111 = 255
255.255.255.128 = 11111111.11111111.11111111.10000000 =>( 25 bits 1 .. 7 bits 0 ) => 1111111 = 127
http://zeus.fh-brandenburg.de/~ihno/doc/lehre/internet/ip_eng.html
![clip_image001[22] clip_image001[22]](http://examgod.com/l2pimages/02fd51a724ed_83C8/clip_image00122_thumb.jpg)
QUESTION 112
You plan to deploy a DHCP server that will support four subnets. The subnets will be configured as shown in the following table.
![clip_image001[24] clip_image001[24]](http://examgod.com/l2pimages/02fd51a724ed_83C8/clip_image00124_thumb.jpg)
You need to identify which network ID you should use for each subnet.
What should you identify? To answer, drag the appropriate network ID to the each subnet in the answer area.
![clip_image001[26] clip_image001[26]](http://examgod.com/l2pimages/02fd51a724ed_83C8/clip_image00126_thumb.jpg)
Answer:
![clip_image001[28] clip_image001[28]](http://examgod.com/l2pimages/02fd51a724ed_83C8/clip_image00128_thumb.jpg)
Explanation:
http://zeus.fh-brandenburg.de/~ihno/doc/lehre/internet/ip_eng.html
![clip_image001[30] clip_image001[30]](http://examgod.com/l2pimages/02fd51a724ed_83C8/clip_image00130_thumb.jpg)
QUESTION 113
You work as a senior administrator at L2P.com. The L2P.com network consists of a single domain named L2P.com. All servers on the L2P.com network have Windows Server 2012 R2 installed, and all workstations have Windows 8 installed.
You are running a training exercise for junior administrators. You are currently discussing a Windows PowerShell cmdlet that activates previously de-activated firewall rules.
Which of the following is the cmdlet being discussed?
A. Set-NetFirewallRule
B. Enable-NetFirewallRule
C. Set-NetIPsecRule
D. Enable-NetIPsecRule
Answer: B
Explanation:
Enable-NetFirewallRule – Enables a previously disabled firewall rule.
http://technet.microsoft.com/en-us/library/cc990290(v=ws.10).aspx http://technet.microsoft.com/en-us/library/jj574205.aspx
http://mikefrobbins.com/2013/02/28/use-powershell-to-remotely-enable-firewall-exceptions-on-windows- server-2012/
http://technet.microsoft.com/en-us/library/jj554869%28v=wps.620%29.aspx
QUESTION 114
Your network contains a server named Server1 that runs Windows Server 2012 R2. Server1 is located on the same subnet as all of the client computers. A network technician reports that he receives a “Request timed out” error message when he attempts to use the ping utility to connect to Server1 from his client computer. The network technician confirms that he can access resources on Server1 from his client computer.
You need to configure Windows Firewall with Advanced Security on Server1 to allow the ping utility to connect.
Which rule should you enable?
A. File and Printer Sharing (Echo Request – ICMPv4-In)
B. Network Discovery (WSD-In)
C. File and Printer Sharing (NB-Session-In)
D. Network Discovery (SSDP-In)
Answer: A
Explanation:
Ping uses ICMP
Open Control Panel, then select System and Security by clicking on that header Select Windows Firewall, Advanced SettingsIn `Windows Firewall with Advanced security’ click on `Inbound rules’ Scroll down to `File and Printer sharing(Echo request ICMPv4-In).
Right click on the rule and select `Enable rule’
![clip_image001[32] clip_image001[32]](http://examgod.com/l2pimages/02fd51a724ed_83C8/clip_image00132_thumb.jpg)
Make sure that it turns green
![clip_image001[34] clip_image001[34]](http://examgod.com/l2pimages/02fd51a724ed_83C8/clip_image00134_thumb.jpg)
Powershell:
Import-Module NetSecurity
Set-NetFirewallRule -DisplayName “File and Printer Sharing (Echo Request ?ICMPv4-In)”
-enabled True
QUESTION 115
You have a file server named Server1 that runs Windows Server 2012 R2.
You need to ensure that a user named User1 can use Windows Server Backup to create a complete backup of Server1. What should you configure?
A. The local groups by using Computer Management
B. A task by using Authorization Manager
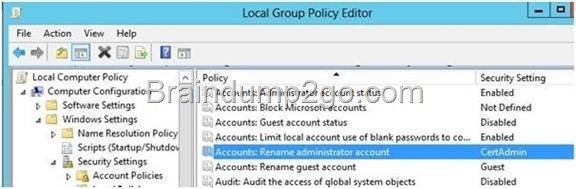
C. The User Rights Assignment by using the Local Group Policy Editor
D. The Role Assignment by using Authorization Manager
Answer: A
Explanation:
A. User needs to be added to local Backup Operator group
B. AzMan is a role-based access control (RBAC) framework that provides an administrative tool to manage authorization policy and a runtime that allows Applications to perform access checks against that policy.
C. User Rights Assignment policies determines which users or groups have logon rights or privileges on the computer
D. AzMan is a role-based access control (RBAC) framework that provides an administrative tool to manage authorization policy and a runtime that allows Applications to perform access checks against that policy.
http://technet.microsoft.com/en-us/library/cc780182(v=ws.10).aspx
http://msdn.microsoft.com/en-us/library/bb897401.aspx
QUESTION 116
Your network contains a production Active Directory forest named contoso.com and a test Active Directory forest named contoso.test. A trust relationship does not exist between the forests. In the contoso.test domain, you create a backup of a Group Policy object (GPO) named GPO1. You transfer the backup of GPO1 to a domain controller in the contoso.com domain.
You need to create a GPO in contoso.com based on the settings of GPO1. You must achieve this goal by using the minimum amount of Administrative effort.
What should you do?
A. From Windows PowerShell, run the Get-GPO cmdlet and the Copy- GPO cmdlet.
B. From Windows PowerShell, run the New-GPO cmdlet and the Import- GPO cmdlet.
C. From Group Policy Management, create a new starter GPO. Right-click the new starter GPO, and then
click Restore from Backup.
D. From Group Policy Management, right-click the Croup Policy Objects container, and then click Manage
Backups.
Answer: B
Explanation:
A. Copy-GPO requires domain trust / copy from one domain to another domain within the same forest. B. The Import-GPO cmdlet imports the settings from a GPO backup into a specified target GPO. Thetarget GPO can be in a different domain or forest than that from which the backup was made and itdoes not have to exist prior to the operation.
C.
D: You can also restore GPOs. This operation takes a backed-up GPO and restores it to the same domain from rom the GPO’s original
which it was backed up. You cannot restore a GPO from backup into a domain different f domain.
The New-GPO cmdlet creates a new GPO with a specified name. By default, the newly created GPO is not linked to a site, domain, or organizational unit (OU). The Import-GPO cmdlet imports the settings from a GPO backup into a specified target GPO. The target GPO can be in a different domain or forest than that from which the backup was made and it does not have to exist prior to the operation.
The Restore-GPO cmdlet restores a GPO backup to the original domain from which it was saved. If the original domain is not available, or if the GPO no longer exists in the domain, the cmdlet fails.
http://technet.microsoft.com/en-us/library/cc781458(v=WS.10).aspx http://technet.microsoft.com/en-us/library/hh967461.aspx
http://technet.microsoft.com/en-us/library/ee461050.aspx
http://technet.microsoft.com/en-us/library/ee461044.aspx
http://blogs.technet.com/b/askpfeplat/archive/2012/11/04/windows-server-2012-the-new-and-improved- group-policy-management-console.aspx
QUESTION 117
Your network contains an active directory forest. The forest functional level is Windows server
2012. The forest contains a single domain. The domain contains a member server named
Server1 that run windows server 2012. You purchase a network scanner named Scanner1 that
supports Web Services on Devices (WDS). You need to share the network scanner on Server1
Which server role should you install on Server1?
A. Web Server (IIS)
B. Fax Server
C. File and Storage Services
D. Print and Document Services
Answer: D
Explanation:
Print and Document Services enables you to centralize print server and network printer tasks. With this role, you can also receive scanned documents from network scanners and route the documents to a shared network resource, Windows SharePoint Services site, or email addresses. Windows Server 2012 uses Web Services on Devices (WSD) technologies to integrate scanning devices into the system
http://technet.microsoft.com/en-us/library/hh831468.aspx
http://technet.microsoft.com/en-us/library/jj134196.aspx
QUESTION 118
Your network contains an Active Directory forest named contoso.com. The forest contains a child domain named europe.contoso.com. The europe.contoso.com child domain contains a server named Server1 that runs Windows Server 2012 R2. You install the DHCP Server server role on Server1. You have access to the administrative accounts shown in the following table.
![clip_image001[36] clip_image001[36]](http://examgod.com/l2pimages/02fd51a724ed_83C8/clip_image00136_thumb.jpg)
You need to authorize Server1. Which user account should you use?
A. Admin1
B. Admin2
C. Admin3
D. Admin4
Answer: D
Explanation:
A. Local account can’t be used
B. Authorization needs to happen in contoso.com and must be aEnt Admin
C. Authorization needs to happen in contoso.com and must be aEnt Admin
D. Correct domain and is a member of Ent Admin’s
http://technet.microsoft.com/en-us/library/cc759688(v=ws.10).aspx
QUESTION 119
Your network contains a server named Server1 that runs Windows Server 2012 R2. App1 has the Print and Document Services server role installed. All client computers run Windows 8. The network contains a network-attached print device named Printer1. From App1, you share Printer1. You need to ensure that users who have connected to Printer1 previously can print to Printer1 if App1 fails.
What should you configure?
To answer, select the appropriate option in the answer area.
![clip_image002[6] clip_image002[6]](http://examgod.com/l2pimages/02fd51a724ed_83C8/clip_image0026_thumb.jpg)
Answer:
![clip_image002[8] clip_image002[8]](http://examgod.com/l2pimages/02fd51a724ed_83C8/clip_image0028_thumb.jpg)
Explanation:
Branch Office Direct Printing can reduce Wide Area Network (WAN) usage by printing directly to a print device instead of a server print queue. This feature can be enabled or disabled on a per printer basis and is transparent to the user. It is enabled by an administrator using the Print Management Console or Windows PowerShell on the server.
The printer information is cached in the branch office, so that if the print server is unavailable for some reason (for example if the WAN link to the data center is down), then it is still possible for the user to print.
Branch Office Direct Printing requires the following operating systems:
Windows Server 2012
Windows 8
http://technet.microsoft.com/en-us/library/jj134156.aspx
QUESTION 120
You have a server named Server1. Server1 runs Windows Server 2012 R2. Server1 has two network adapters and is located in a perimeter network. You need to install a DHCP Relay Agent on Server1. Which node should you use to add the DHCP Relay Agent? To answer, select the appropriate node in the answer area.
![clip_image001[38] clip_image001[38]](http://examgod.com/l2pimages/02fd51a724ed_83C8/clip_image00138_thumb.jpg)
Answer:
![clip_image001[40] clip_image001[40]](http://examgod.com/l2pimages/02fd51a724ed_83C8/clip_image00140_thumb.jpg)
Explanation:
Membership in the local Administrators group, or equivalent, is the minimum required to complete this procedure.
To configure the IPv4 DHCP relay agent
1. In the Routing and Remote Access MMC snap-in, expand IPv4, right-click General, and then click New Routing Protocol.
2. In the New Routing Protocol dialog box, select DHCPv4 Relay Agent, and then click OK.
3. In the navigation pane, right-click DHCPv4 Relay Agent, and then click New Interface.
4. Add the network interfaces on which the server might receive DHCPv4 requests that you want to send to the DHCP server. Right-click DHCPv4 Relay Agent, click New Interface, select the appropriate network interface, and then click OK.
5. In the DHCP Relay Properties dialog box, select Relay DHCP packets, and then click OK.
6. In the navigation pane, right-click DHCP Relay Agent, and then click Properties.
7. On the General tab, enter the IPv4 address of the DHCP servers that you want to provide DHCP services for the RRAS server’s clients, click Add, and then click OK.
http://technet.microsoft.com/en-us/library/dd469685.aspx
Passing Microsoft 70-410 Exam successfully in a short time! Just using Braindump2go’s Latest Microsoft 70-410 Dump:http://www.braindump2go.com/70-410.html
![clip_image001[4] clip_image001[4]](http://examgod.com/l2pimages/02fd51a724ed_83C8/clip_image0014_thumb.jpg)
![clip_image001[6] clip_image001[6]](http://examgod.com/l2pimages/02fd51a724ed_83C8/clip_image0016_thumb.jpg)
![clip_image001[8] clip_image001[8]](http://examgod.com/l2pimages/02fd51a724ed_83C8/clip_image0018_thumb.jpg)
![clip_image001[10] clip_image001[10]](http://examgod.com/l2pimages/02fd51a724ed_83C8/clip_image00110_thumb.jpg)
![clip_image001[12] clip_image001[12]](http://examgod.com/l2pimages/02fd51a724ed_83C8/clip_image00112_thumb.jpg)
![clip_image001[14] clip_image001[14]](http://examgod.com/l2pimages/02fd51a724ed_83C8/clip_image00114_thumb.jpg)
![clip_image001[16] clip_image001[16]](http://examgod.com/l2pimages/02fd51a724ed_83C8/clip_image00116_thumb.jpg)
![clip_image001[18] clip_image001[18]](http://examgod.com/l2pimages/02fd51a724ed_83C8/clip_image00118_thumb.jpg)
![clip_image001[20] clip_image001[20]](http://examgod.com/l2pimages/02fd51a724ed_83C8/clip_image00120_thumb.jpg)
![clip_image002[4] clip_image002[4]](http://examgod.com/l2pimages/02fd51a724ed_83C8/clip_image0024_thumb.jpg)
![clip_image001[64] clip_image001[64]](http://examgod.com/l2pimages/6aff33333266_8257/clip_image00164_thumb.jpg)
![clip_image001[66] clip_image001[66]](http://examgod.com/l2pimages/6aff33333266_8257/clip_image00166_thumb.jpg)
![clip_image001[68] clip_image001[68]](http://examgod.com/l2pimages/6aff33333266_8257/clip_image00168_thumb.jpg)
![clip_image002[52] clip_image002[52]](http://examgod.com/l2pimages/6aff33333266_8257/clip_image00252_thumb.jpg)
![clip_image001[70] clip_image001[70]](http://examgod.com/l2pimages/6aff33333266_8257/clip_image00170_thumb.jpg)
![clip_image001[72] clip_image001[72]](http://examgod.com/l2pimages/6aff33333266_8257/clip_image00172_thumb.jpg)
![clip_image001[74] clip_image001[74]](http://examgod.com/l2pimages/6aff33333266_8257/clip_image00174_thumb.jpg)
![clip_image001[76] clip_image001[76]](http://examgod.com/l2pimages/6aff33333266_8257/clip_image00176_thumb.jpg)
![clip_image001[56] clip_image001[56]](http://examgod.com/l2pimages/6aff33333266_8257/clip_image00156_thumb.jpg)
![clip_image002[6] clip_image002[6]](http://examgod.com/l2pimages/6aff33333266_8257/clip_image0026_thumb.gif)
![clip_image002[46] clip_image002[46]](http://examgod.com/l2pimages/6aff33333266_8257/clip_image00246_thumb.jpg)
![clip_image001[58] clip_image001[58]](http://examgod.com/l2pimages/6aff33333266_8257/clip_image00158_thumb.jpg)
![clip_image001[60] clip_image001[60]](http://examgod.com/l2pimages/6aff33333266_8257/clip_image00160_thumb.jpg)
![clip_image002[8] clip_image002[8]](http://examgod.com/l2pimages/6aff33333266_8257/clip_image0028_thumb.gif)
![clip_image001[62] clip_image001[62]](http://examgod.com/l2pimages/6aff33333266_8257/clip_image00162_thumb.jpg)
![clip_image002[10] clip_image002[10]](http://examgod.com/l2pimages/6aff33333266_8257/clip_image00210_thumb.gif)
![clip_image002[48] clip_image002[48]](http://examgod.com/l2pimages/6aff33333266_8257/clip_image00248_thumb.jpg)
![clip_image002[50] clip_image002[50]](http://examgod.com/l2pimages/6aff33333266_8257/clip_image00250_thumb.jpg)
![clip_image002[40] clip_image002[40]](http://examgod.com/l2pimages/6aff33333266_8257/clip_image00240_thumb.jpg)
![clip_image002[42] clip_image002[42]](http://examgod.com/l2pimages/6aff33333266_8257/clip_image00242_thumb.jpg)
![clip_image001[48] clip_image001[48]](http://examgod.com/l2pimages/6aff33333266_8257/clip_image00148_thumb.jpg)
![clip_image001[50] clip_image001[50]](http://examgod.com/l2pimages/6aff33333266_8257/clip_image00150_thumb.jpg)
![clip_image001[52] clip_image001[52]](http://examgod.com/l2pimages/6aff33333266_8257/clip_image00152_thumb.jpg)
![clip_image001[54] clip_image001[54]](http://examgod.com/l2pimages/6aff33333266_8257/clip_image00154_thumb.jpg)
![clip_image002[44] clip_image002[44]](http://examgod.com/l2pimages/6aff33333266_8257/clip_image00244_thumb.jpg)
![clip_image001[46] clip_image001[46]](http://examgod.com/l2pimages/6aff33333266_8257/clip_image00146_thumb.jpg)
![clip_image002[36] clip_image002[36]](http://examgod.com/l2pimages/6aff33333266_8257/clip_image00236_thumb.jpg)
![clip_image002[38] clip_image002[38]](http://examgod.com/l2pimages/6aff33333266_8257/clip_image00238_thumb.jpg)
![clip_image001[34] clip_image001[34]](http://examgod.com/l2pimages/6aff33333266_8257/clip_image00134_thumb.jpg)
![clip_image001[36] clip_image001[36]](http://examgod.com/l2pimages/6aff33333266_8257/clip_image00136_thumb.jpg)
![clip_image002[26] clip_image002[26]](http://examgod.com/l2pimages/6aff33333266_8257/clip_image00226_thumb.jpg)
![clip_image002[28] clip_image002[28]](http://examgod.com/l2pimages/6aff33333266_8257/clip_image00228_thumb.jpg)
![clip_image002[30] clip_image002[30]](http://examgod.com/l2pimages/6aff33333266_8257/clip_image00230_thumb.jpg)
![clip_image001[38] clip_image001[38]](http://examgod.com/l2pimages/6aff33333266_8257/clip_image00138_thumb.jpg)
![clip_image002[32] clip_image002[32]](http://examgod.com/l2pimages/6aff33333266_8257/clip_image00232_thumb.jpg)
![clip_image001[40] clip_image001[40]](http://examgod.com/l2pimages/6aff33333266_8257/clip_image00140_thumb.jpg)
![clip_image001[42] clip_image001[42]](http://examgod.com/l2pimages/6aff33333266_8257/clip_image00142_thumb.jpg)
![clip_image001[44] clip_image001[44]](http://examgod.com/l2pimages/6aff33333266_8257/clip_image00144_thumb.jpg)
![clip_image002[34] clip_image002[34]](http://examgod.com/l2pimages/6aff33333266_8257/clip_image00234_thumb.jpg)
![clip_image002[20] clip_image002[20]](http://examgod.com/l2pimages/6aff33333266_8257/clip_image00220_thumb.jpg)
![clip_image002[22] clip_image002[22]](http://examgod.com/l2pimages/6aff33333266_8257/clip_image00222_thumb.jpg)
![clip_image002[24] clip_image002[24]](http://examgod.com/l2pimages/6aff33333266_8257/clip_image00224_thumb.jpg)
![clip_image001[26] clip_image001[26]](http://examgod.com/l2pimages/6aff33333266_8257/clip_image00126_thumb.jpg)
![clip_image001[28] clip_image001[28]](http://examgod.com/l2pimages/6aff33333266_8257/clip_image00128_thumb.jpg)
![clip_image001[30] clip_image001[30]](http://examgod.com/l2pimages/6aff33333266_8257/clip_image00130_thumb.jpg)
![clip_image001[32] clip_image001[32]](http://examgod.com/l2pimages/6aff33333266_8257/clip_image00132_thumb.jpg)
![clip_image002[12] clip_image002[12]](http://examgod.com/l2pimages/6aff33333266_8257/clip_image00212_thumb.jpg)
![clip_image001[10] clip_image001[10]](http://examgod.com/l2pimages/6aff33333266_8257/clip_image00110_thumb.jpg)
![clip_image002[14] clip_image002[14]](http://examgod.com/l2pimages/6aff33333266_8257/clip_image00214_thumb.jpg)
![clip_image001[12] clip_image001[12]](http://examgod.com/l2pimages/6aff33333266_8257/clip_image00112_thumb.jpg)
![clip_image001[14] clip_image001[14]](http://examgod.com/l2pimages/6aff33333266_8257/clip_image00114_thumb.jpg)
![clip_image001[16] clip_image001[16]](http://examgod.com/l2pimages/6aff33333266_8257/clip_image00116_thumb.jpg)
![clip_image001[18] clip_image001[18]](http://examgod.com/l2pimages/6aff33333266_8257/clip_image00118_thumb.jpg)
![clip_image002[16] clip_image002[16]](http://examgod.com/l2pimages/6aff33333266_8257/clip_image00216_thumb.jpg)
![clip_image001[20] clip_image001[20]](http://examgod.com/l2pimages/6aff33333266_8257/clip_image00120_thumb.jpg)
![clip_image001[22] clip_image001[22]](http://examgod.com/l2pimages/6aff33333266_8257/clip_image00122_thumb.jpg)
![clip_image001[24] clip_image001[24]](http://examgod.com/l2pimages/6aff33333266_8257/clip_image00124_thumb.jpg)
![clip_image002[18] clip_image002[18]](http://examgod.com/l2pimages/6aff33333266_8257/clip_image00218_thumb.jpg)
![clip_image001[4] clip_image001[4]](http://examgod.com/l2pimages/6aff33333266_8257/clip_image0014_thumb.jpg)
![clip_image001[6] clip_image001[6]](http://examgod.com/l2pimages/6aff33333266_8257/clip_image0016_thumb.jpg)
![clip_image002[4] clip_image002[4]](http://examgod.com/l2pimages/6aff33333266_8257/clip_image0024_thumb.jpg)
![clip_image002[6] clip_image002[6]](http://examgod.com/l2pimages/6aff33333266_8257/clip_image0026_thumb.jpg)
![clip_image001[8] clip_image001[8]](http://examgod.com/l2pimages/6aff33333266_8257/clip_image0018_thumb.jpg)
![clip_image002[8] clip_image002[8]](http://examgod.com/l2pimages/6aff33333266_8257/clip_image0028_thumb.jpg)
![clip_image001[10] clip_image001[10]](http://examgod.com/l2pimages/bca8ca93375f_7FA7/clip_image00110_thumb_3.jpg)
![clip_image001[12] clip_image001[12]](http://examgod.com/l2pimages/bca8ca93375f_7FA7/clip_image00112_thumb.jpg)
![clip_image001[14] clip_image001[14]](http://examgod.com/l2pimages/bca8ca93375f_7FA7/clip_image00114_thumb.jpg)
![clip_image001[16] clip_image001[16]](http://examgod.com/l2pimages/bca8ca93375f_7FA7/clip_image00116_thumb.jpg)
![clip_image001[18] clip_image001[18]](http://examgod.com/l2pimages/bca8ca93375f_7FA7/clip_image00118_thumb.jpg)
![clip_image001[20] clip_image001[20]](http://examgod.com/l2pimages/bca8ca93375f_7FA7/clip_image00120_thumb.jpg)
![clip_image001[22] clip_image001[22]](http://examgod.com/l2pimages/bca8ca93375f_7FA7/clip_image00122_thumb.jpg)
![clip_image001[24] clip_image001[24]](http://examgod.com/l2pimages/bca8ca93375f_7FA7/clip_image00124_thumb.jpg)
![clip_image002[6] clip_image002[6]](http://examgod.com/l2pimages/bca8ca93375f_7FA7/clip_image0026_thumb_3.jpg)
![clip_image001[26] clip_image001[26]](http://examgod.com/l2pimages/bca8ca93375f_7FA7/clip_image00126_thumb.jpg)
![clip_image001[4] clip_image001[4]](http://examgod.com/l2pimages/bca8ca93375f_7FA7/clip_image0014_thumb_3.jpg)
![clip_image002[4] clip_image002[4]](http://examgod.com/l2pimages/bca8ca93375f_7FA7/clip_image0024_thumb_3.jpg)
![clip_image001[6] clip_image001[6]](http://examgod.com/l2pimages/bca8ca93375f_7FA7/clip_image0016_thumb_3.jpg)
![clip_image001[8] clip_image001[8]](http://examgod.com/l2pimages/bca8ca93375f_7FA7/clip_image0018_thumb_3.jpg)
![clip_image001[9] clip_image001[9]](http://examgod.com/l2pimages/bca8ca93375f_7FA7/clip_image0019_thumb.jpg)
![clip_image002[17] clip_image002[17]](http://examgod.com/l2pimages/bca8ca93375f_7FA7/clip_image00217_thumb.jpg)
![clip_image001[11] clip_image001[11]](http://examgod.com/l2pimages/bca8ca93375f_7FA7/clip_image00111_thumb.jpg)
![clip_image001[13] clip_image001[13]](http://examgod.com/l2pimages/bca8ca93375f_7FA7/clip_image00113_thumb.jpg)
![clip_image001[15] clip_image001[15]](http://examgod.com/l2pimages/bca8ca93375f_7FA7/clip_image00115_thumb.jpg)
![clip_image001[17] clip_image001[17]](http://examgod.com/l2pimages/bca8ca93375f_7FA7/clip_image00117_thumb.jpg)
![clip_image001[19] clip_image001[19]](http://examgod.com/l2pimages/bca8ca93375f_7FA7/clip_image00119_thumb.jpg)
![clip_image002[19] clip_image002[19]](http://examgod.com/l2pimages/bca8ca93375f_7FA7/clip_image00219_thumb.jpg)
![clip_image002[21] clip_image002[21]](http://examgod.com/l2pimages/bca8ca93375f_7FA7/clip_image00221_thumb.jpg)
![clip_image001[21] clip_image001[21]](http://examgod.com/l2pimages/bca8ca93375f_7FA7/clip_image00121_thumb.jpg)
![clip_image001[23] clip_image001[23]](http://examgod.com/l2pimages/bca8ca93375f_7FA7/clip_image00123_thumb.jpg)
![clip_image001[25] clip_image001[25]](http://examgod.com/l2pimages/bca8ca93375f_7FA7/clip_image00125_thumb.jpg)
![clip_image002[1] clip_image002[1]](http://examgod.com/l2pimages/bca8ca93375f_7FA7/clip_image0021_thumb.jpg)
![clip_image002[3] clip_image002[3]](http://examgod.com/l2pimages/bca8ca93375f_7FA7/clip_image0023_thumb.jpg)
![clip_image002[5] clip_image002[5]](http://examgod.com/l2pimages/bca8ca93375f_7FA7/clip_image0025_thumb.jpg)
![clip_image001[1] clip_image001[1]](http://examgod.com/l2pimages/bca8ca93375f_7FA7/clip_image0011_thumb.jpg)
![clip_image002[7] clip_image002[7]](http://examgod.com/l2pimages/bca8ca93375f_7FA7/clip_image0027_thumb.jpg)
![clip_image002[9] clip_image002[9]](http://examgod.com/l2pimages/bca8ca93375f_7FA7/clip_image0029_thumb.jpg)
![clip_image002[11] clip_image002[11]](http://examgod.com/l2pimages/bca8ca93375f_7FA7/clip_image00211_thumb.jpg)
![clip_image002[13] clip_image002[13]](http://examgod.com/l2pimages/bca8ca93375f_7FA7/clip_image00213_thumb.jpg)
![clip_image002[15] clip_image002[15]](http://examgod.com/l2pimages/bca8ca93375f_7FA7/clip_image00215_thumb.jpg)
![clip_image001[3] clip_image001[3]](http://examgod.com/l2pimages/bca8ca93375f_7FA7/clip_image0013_thumb.jpg)
![clip_image001[5] clip_image001[5]](http://examgod.com/l2pimages/bca8ca93375f_7FA7/clip_image0015_thumb.jpg)
![clip_image001[7] clip_image001[7]](http://examgod.com/l2pimages/bca8ca93375f_7FA7/clip_image0017_thumb.jpg)