March/2020 New CCNA 200-301 Exam Dumps with PDF and VCE New Released Today! Following are some new 200-301 Real Exam Questions!
New Question
Which two values or settings must be entered when configuring a new WLAN in the Cisco Wireless LAN Controller GUI? (Choose two)
A. management interface settings
B. QoS settings
C. Ip address of one or more access points
D. SSID
E. Profile name
Correct Answer: DE
New Question
What are two benefits of network automation? (Choose two)
A. reduced operational costs
B. reduced hardware footprint
C. faster changes with more reliable results
D. fewer network failures
E. increased network security
Correct Answer: AC
New Question
Which command prevents passwords from being stored in the configuration as plaintext on a router or switch?
A. enable secret
B. service password-encryption
C. username Cisco password encrypt
D. enable password
Correct Answer: B
New Question
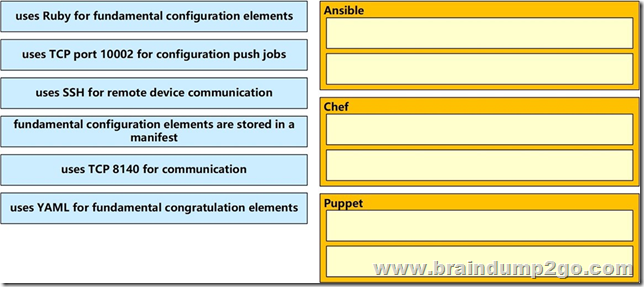
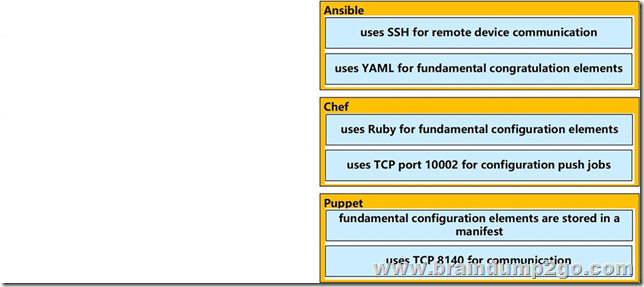
Drag and Drop Question
Drag drop the descriptions from the left on to the correct configuration-management technologies on the right.
Select and Place:
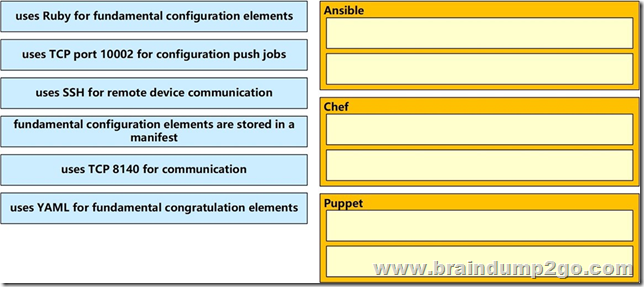
Correct Answer:
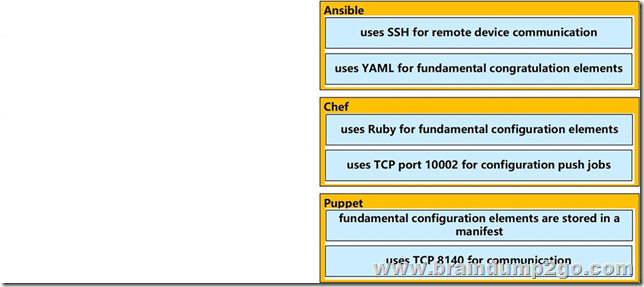
Explanation:
The focus of Ansible is to be streamlined and fast, and to require no node agent installation. Thus, Ansible performs all functions over SSH. Ansible is built on Python, in contrast to the Ruby foundation of Puppet and Chef. TCP port 10002 is the command port. It may be configured in the Chef Push Jobs configuration file . This port allows Chef Push Jobs clients to communicate with the Chef Push Jobs server.
Puppet is an open-source configuration management solution, which is built with Ruby and offers custom Domain Specific Language (DSL) and Embedded Ruby (ERB) templates to create custom Puppet language files, offering a declarative- paradigm programming approach.
A Puppet piece of code is called a manifest, and is a file with .pp extension.
New Question
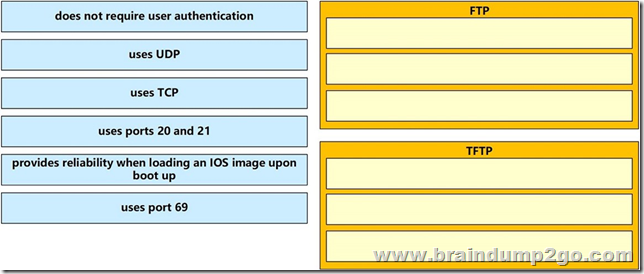
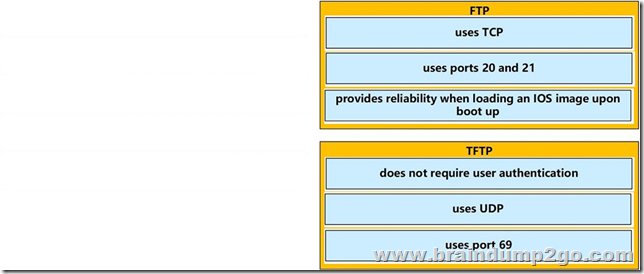
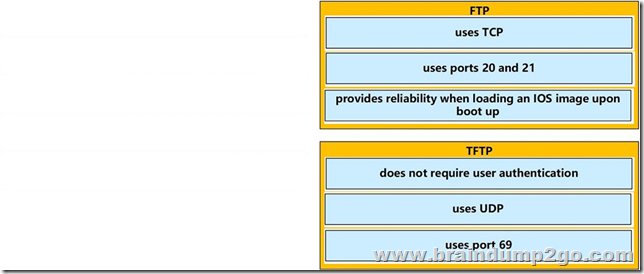
Drag and Drop Question
Drag and drop the descriptions of file-transfer protocols from the left onto the correct protocols on the right.
Select and Place:
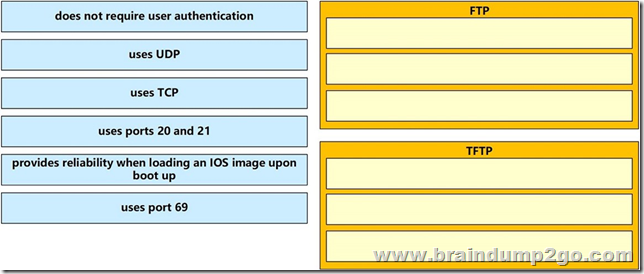
Correct Answer:
New Question
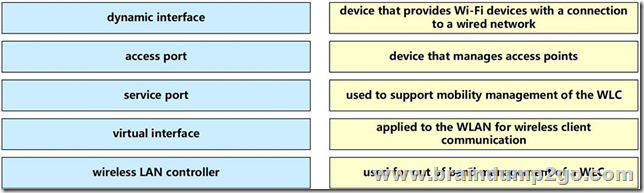
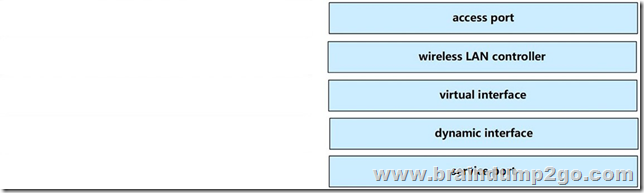
Drag and Drop Question
Drag and drop the WLAN components from the left onto the correct descriptions on the right.
Select and Place:
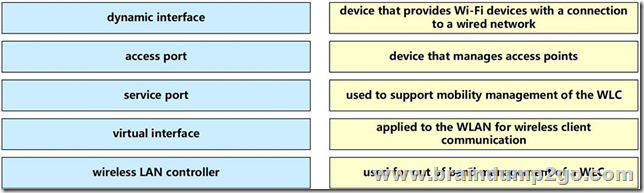
Correct Answer:
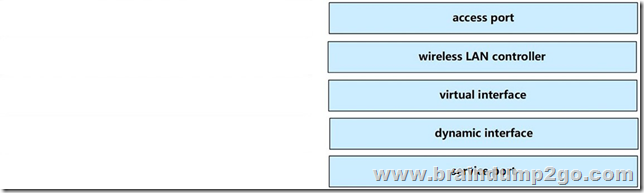
Explanation:
The service port can be used management purposes, primarily for out-of-band management. However, AP management traffic is not possible across the service port. In most cases, the service port is used as a “last resort” means of accessing the controller GUI for management purposes. For example, in the case where the system distribution ports on the controller are down or their communication to the wired network is otherwise degraded.
A dynamic interface with the Dynamic AP Management option enabled is used as the tunnel source for packets from the controller to the access point and as the destination for CAPWAP packets from the access point to the controller.
The virtual interface is used to support mobility management, Dynamic Host Configuration Protocol (DHCP) relay, and embedded Layer 3 security such as guest web authentication. It also maintains the DNS gateway host name used by Layer 3 security and mobility managers to verify the source of certificates when Layer 3 web authorization is enabled.
Reference: https://www.cisco.com/c/en/us/td/docs/wireless/controller/8-5/config-guide/b_cg85/ports_and_interfaces.html
New Question
Drag and Drop Question
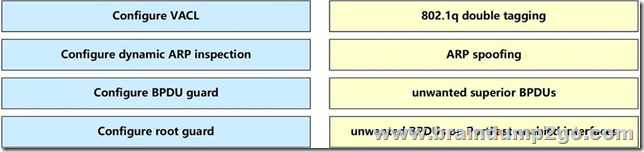
Drag and drop the threat-mitigation techniques from the left onto the types of threat or attack they mitigate on the right.
Select and Place:
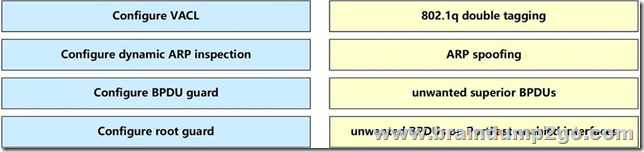
Correct Answer:

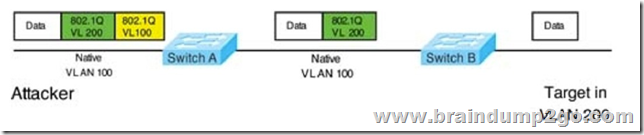
Double-Tagging attack:
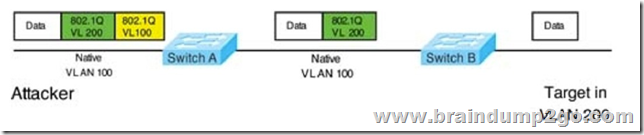
In this attack, the attacking computer generates frames with two 802.1Q tags. The first tag matches the native VLAN of the trunk port (VLAN 10 in this case), and the second matches the VLAN of a host it wants to attack (VLAN 20).
When the packet from the attacker reaches Switch A, Switch A only sees the first VLAN 10 and it matches with its native VLAN 10 so this VLAN tag is removed. Switch A forwards the frame out all links with the same native VLAN 10. Switch B receives the frame with an tag of VLAN 20 so it removes this tag and forwards out to the Victim computer.
Note: This attack only works if the trunk (between two switches) has the same native VLAN as the attacker.
To mitigate this type of attack, you can use VLAN access control lists (VACLs, which applies to all traffic within a VLAN. We can use VACL to drop attacker traffic to specific victims/servers) or implement Private VLANs.
ARP attack (like ARP poisoning/spoofing) is a type of attack in which a malicious actor sends falsified ARP messages over a local area network as ARP allows a gratuitous reply from a host even if an ARP request was not received. This results in the linking of an attacker’s MAC address with the IP address of a legitimate computer or server on the network. This is an attack based on ARP which is at Layer 2. Dynamic ARP inspection (DAI) is a security feature that validates ARP packets in a network which can be used to mitigate this type of attack.
New Question
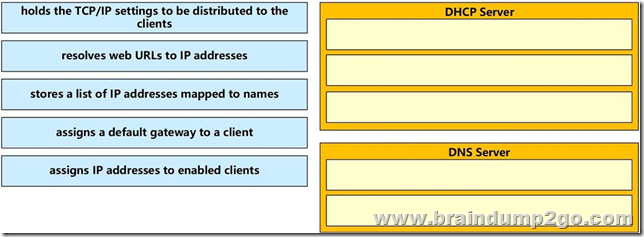
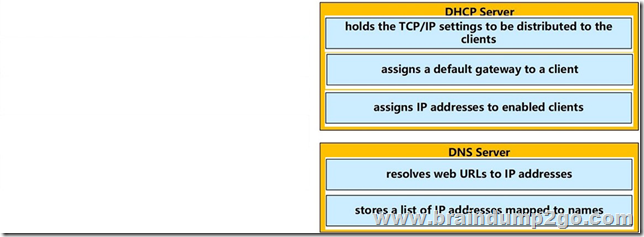
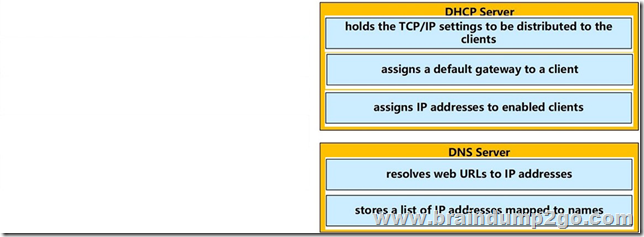
Drag and Drop Question
Drag and drop the functions from the left onto the correct network components on the right.
Select and Place:
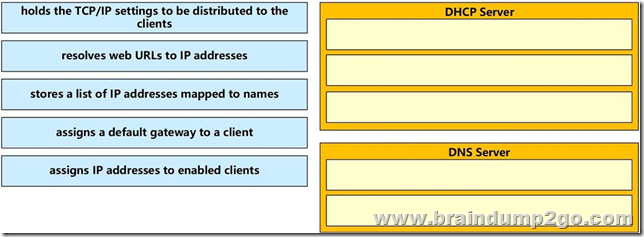
Correct Answer:
New Question
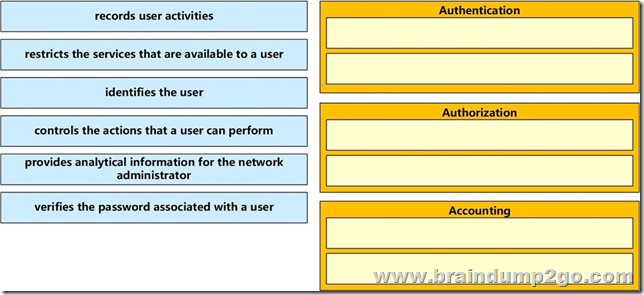
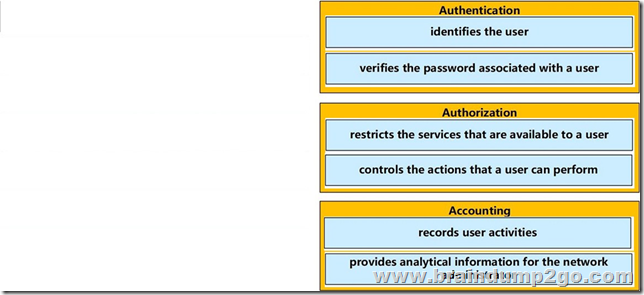
Drag and Drop Question
Drag and drop the AAA functions from the left onto the correct AAA services on the right.
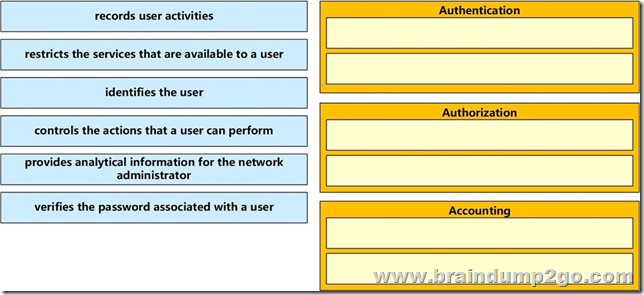
Select and Place:
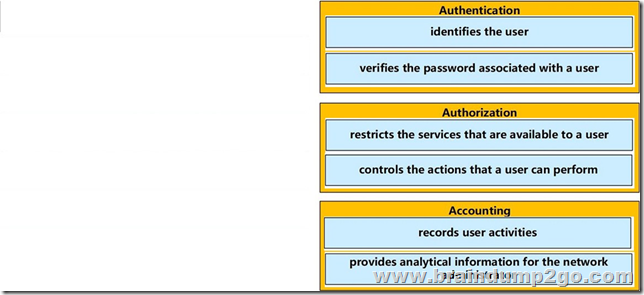
Correct Answer:
New Question
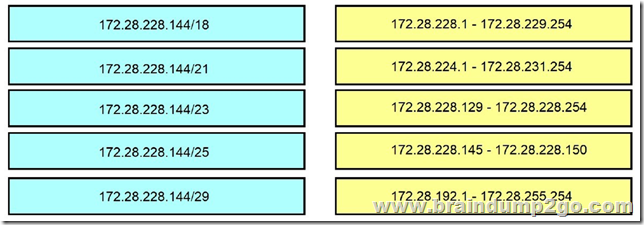
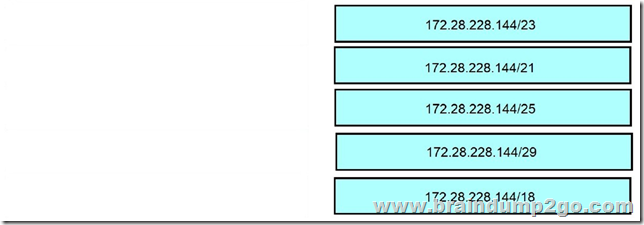
Drag and Drop Question
Drag and drop the IPv4 network subnets from the left onto the correct usable host ranges on the right
Select and Place:
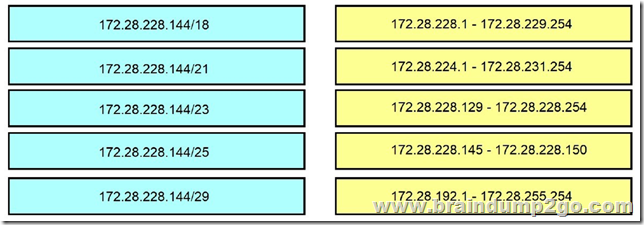
Correct Answer:
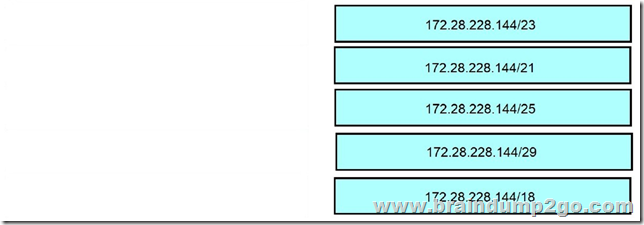
Explanation:
This subnet question requires us to grasp how to subnet very well. To quickly find out the subnet range, we have to find out the increment and the network address of each subnet. Let’s take an example with the subnet 172.28.228.144/18:
From the /18 (= 1100 0000 in the 3rd octet), we find out the increment is 64. Therefore the network address of this subnet must be the greatest multiple of the increment but not greater than the value in the 3rd octet (228). We can find out the 3rd octet of the network address is 192 (because 192 = 64 * 3 and 192 < 228) -> The network address is 172.28.192.0. So the first usable host should be 172.28.192.1 and it matches with the 5th answer on the right. In this case we don’t need to calculate the broadcast address because we found the correct answer.
Let’s take another example with subnet 172.28.228.144/23 -> The increment is 2 (as /23 = 1111 1110 in 3rd octet) -> The 3rd octet of the network address is 228 (because 228 is the multiply of 2 and equal to the 3rd octet) -> The network address is 172.28.228.0 -> The first usable host is 172.28.228.1. It is not necessary but if we want to find out the broadcast address of this subnet, we can find out the next network address, which is 172.28.(228 + the increment number).0 or 172.28.230.0 then reduce 1 bit -> 172.28.229.255 is the broadcast address of our subnet. Therefore the last usable host is 172.28.229.254.
New Question
Drag and Drop Question
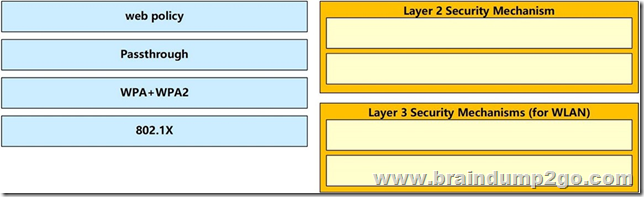
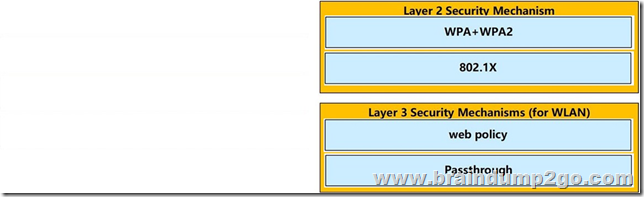
Drag and drop the Cisco Wireless LAN Controller security settings from the left onto the correct security mechanism categories on the right.
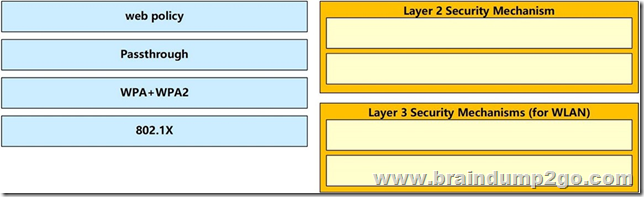
Select and Place:
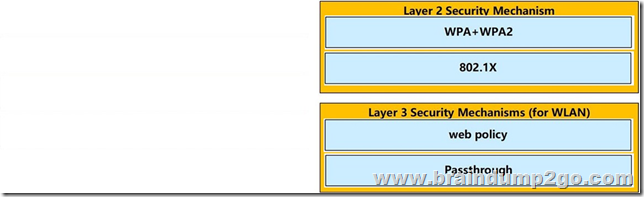
Correct Answer:
Explanation:
Layer 2 Security Mechanism includes WPA+WPA2, 802.1X, Static WEP, CKIP while Layer 3 Security Mechanisms (for WLAN) includes IPSec, VPN Pass-Through, Web Passthrough … Reference: https://www.cisco.com/c/en/us/support/docs/wireless/4400-series-wireless-lan-controllers/106082-wlc-compatibility-matrix.html
Resources from:
1.2020 Latest Braindump2go 200-301 Exam Dumps (PDF & VCE) Free Share:
https://www.braindump2go.com/200-301.html
2.2020 Latest Braindump2go 200-301 PDF and 200-301 VCE Dumps Free Share:
https://drive.google.com/drive/folders/1N579lVwFMNcTo1QgOz_B6__zxBTx36ev?usp=sharing
3.2020 Latest Braindump2go 200-301 PDF and 200-301 VCE Dumps Free Share:
https://od.lk/fl/NDZfMTE3ODI2Nl8
Free Resources from Braindump2go,We Devoted to Helping You 100% Pass All Exams!